A cyber attack can cripple your Southern California business within hours. At Tower Insurance Associates, Inc., we’ve seen firsthand how quickly incidents spiral when companies don’t know what to do next.
This LA cyber claims guide walks you through every step-from the moment you detect a breach to final resolution. You’ll learn what your coverage actually protects, how to file a claim properly, and what to expect during the process.
What Your Cyber Liability Policy Actually Covers
Cyber liability insurance in Southern California covers two distinct categories of losses that standard business policies ignore entirely. First-party coverage pays for your direct costs: forensic investigations that average around $45,000 per incident, data recovery expenses, business interruption losses when your systems are down, crisis management and public relations, and ransom payments if you face extortion.
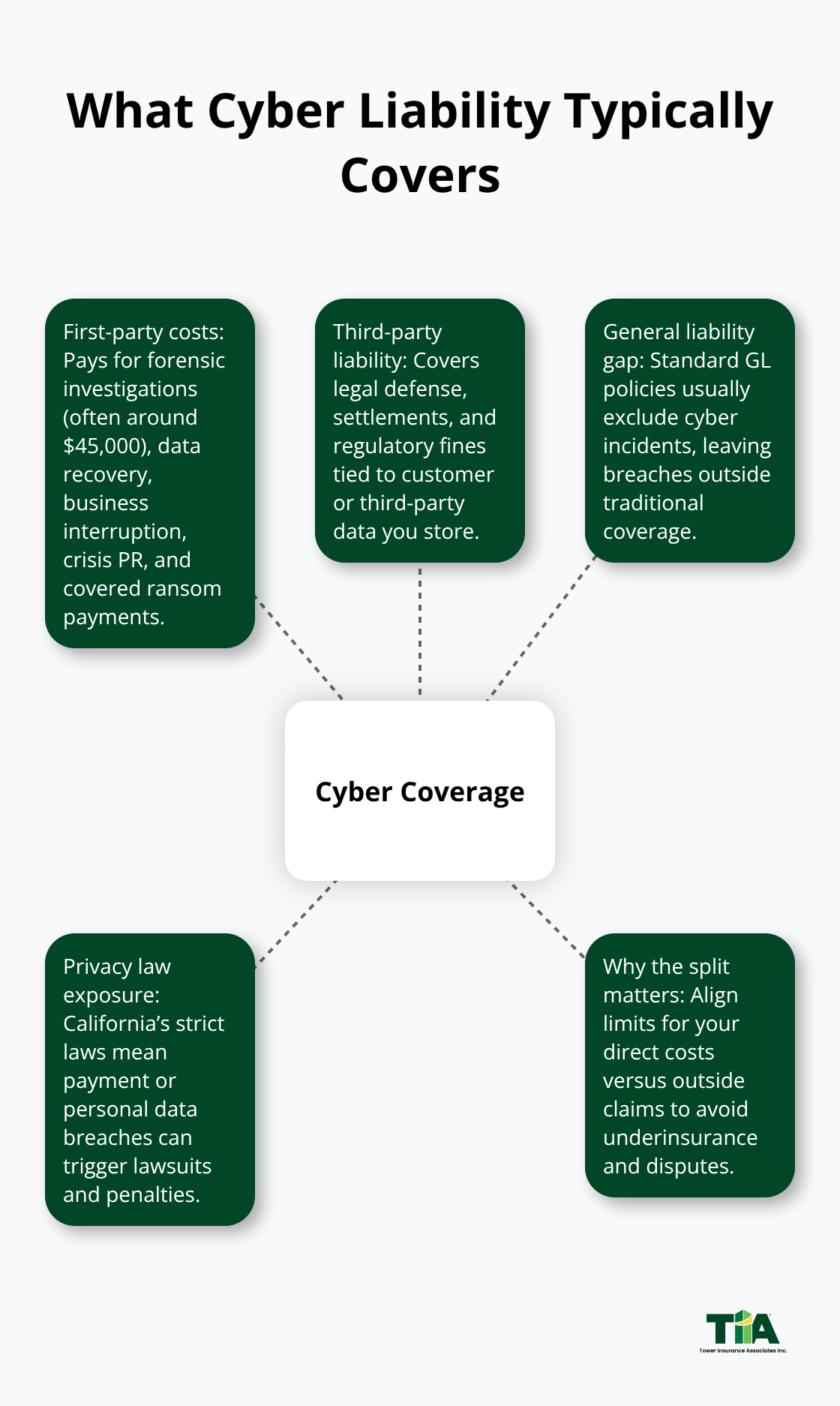
Second-party coverage handles claims from customers and third parties whose data you store, including legal defense costs, settlements, and regulatory fines. This split matters because many Southern California business owners assume their general liability policy covers cyber incidents-it doesn’t. A breach affecting customer payment information or personal data falls outside traditional coverage, leaving you exposed to lawsuits and regulatory penalties under California’s strict privacy laws.
The coverage gaps that hurt most Southern California businesses
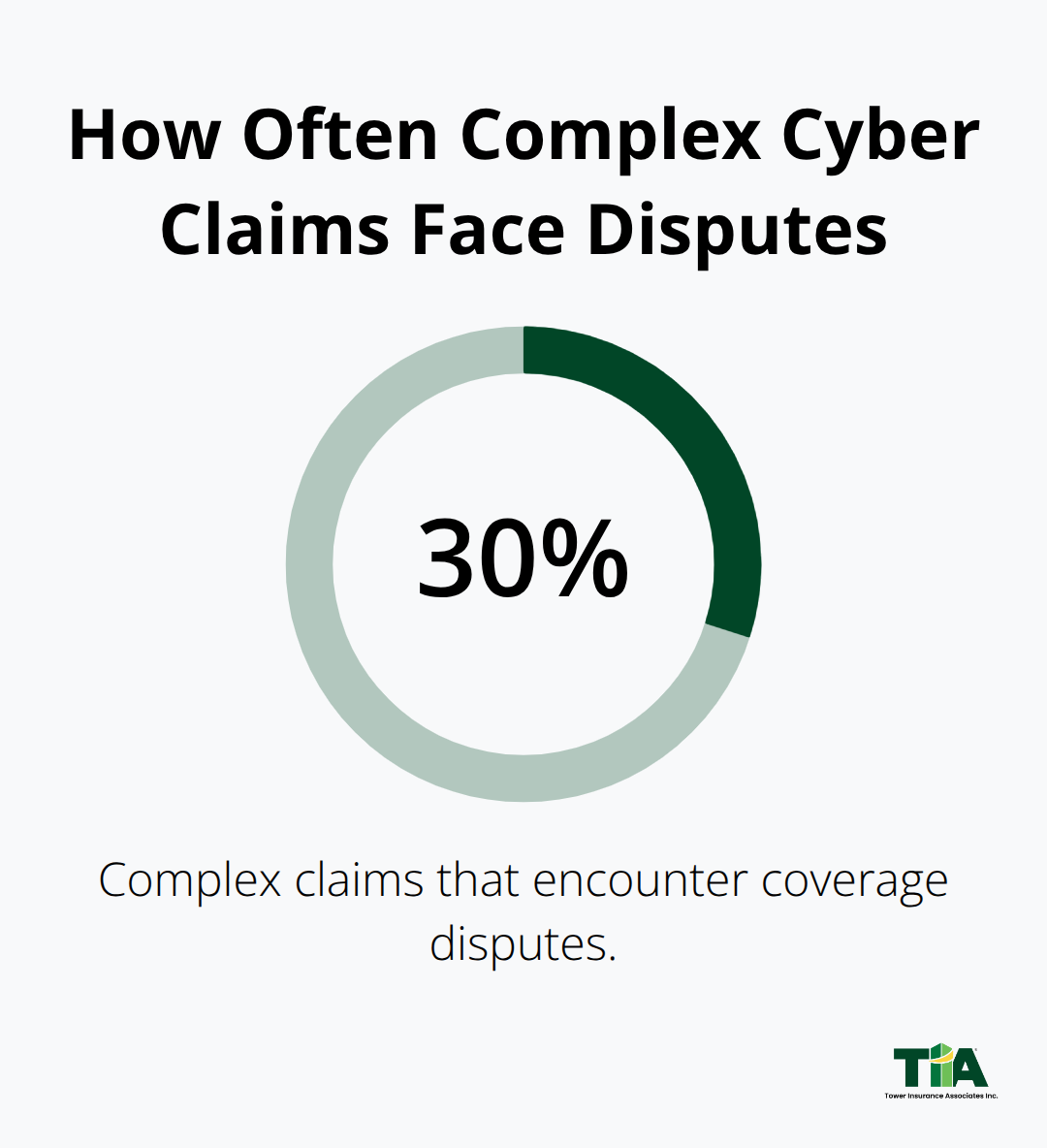
Your policy’s language determines what actually gets paid when a claim happens. Many carriers exclude coverage if you failed to maintain basic security controls like multi-factor authentication or endpoint detection and response. Others deny claims based on prior knowledge clauses: if your company knew about a vulnerability before the attack, they won’t pay. California’s breach notification requirement requires disclosure within 30 calendar days of discovery. If you miss the deadline and the insurer determines your delays caused additional damages, coverage can be denied entirely. The average cyber liability claim in 2024 took 45 to 60 days to process, with coverage disputes occurring in roughly 30 percent of complex claims. This matters because your business needs fast access to forensic experts and legal counsel immediately after an incident, not months later during disputes. Southern California healthcare providers face an additional problem: HIPAA violations can trigger penalties up to $1.5 million per violation category, and many standard cyber policies cap regulatory defense coverage far below that exposure. Retail and e-commerce businesses handling payment card data need PCI DSS compliance built into their coverage, yet half the policies we review lack this specificity.
Why Southern California’s risk profile demands tailored coverage
California’s privacy laws are the strictest in the nation, and the state’s breach costs exceed $4.6 million on average. The Inland Empire experiences higher vulnerability rates because many small firms operate with limited IT resources while handling sensitive customer data. Business email compromise attacks rose 300 percent in the Inland Empire over recent years, yet many policies provide minimal coverage for social engineering losses. Your industry matters tremendously: healthcare practices typically need coverage limits starting around $2 million, while retail operations processing thousands of card transactions monthly face different exposure. A micro business with 1 to 10 employees in Riverside might pay $500 to $1,500 annually for solid coverage, while mid-sized firms with 51 to 100 employees typically invest $2,000 to $8,000. High-risk industries pay 20 to 40 percent above average premiums.
Align your coverage with your actual data exposure
Start by mapping your data flows-identify what customer information you hold, where it lives, who accesses it, and what would happen if it disappeared. That exercise alone reveals whether your current coverage aligns with your actual exposure. Once you understand your data landscape and the coverage gaps in your existing policy, the next critical step involves taking immediate action when an incident occurs. The first hours after a breach determine whether your claim succeeds or fails, and knowing exactly what to do separates businesses that recover quickly from those that face months of disputes and denied coverage.
What to Do in the First 24 Hours After a Breach
The moment you detect a cyber incident, your actions determine whether your claim gets paid and how much damage your business suffers. Most cyber policies require notification to your insurer within 24 to 72 hours of discovery, and missing this deadline can result in automatic claim denial regardless of the incident’s severity.
Isolate systems and contact your insurer immediately
Your first task is to isolate affected systems immediately-disconnect compromised devices from your network, shut down remote access, and prevent the attack from spreading to uncompromised equipment. Do not power down systems without guidance from your insurer’s assigned forensic team, as this can destroy critical evidence needed for investigation and claim validation. Call your insurance provider the moment you confirm a breach, even if details remain unclear. Provide your policy number, a brief description of what happened, the systems involved, and the approximate time of discovery. The insurer will assign a claims handler, provide a list of pre-approved forensic vendors, and issue a reservation of rights letter outlining coverage limitations.
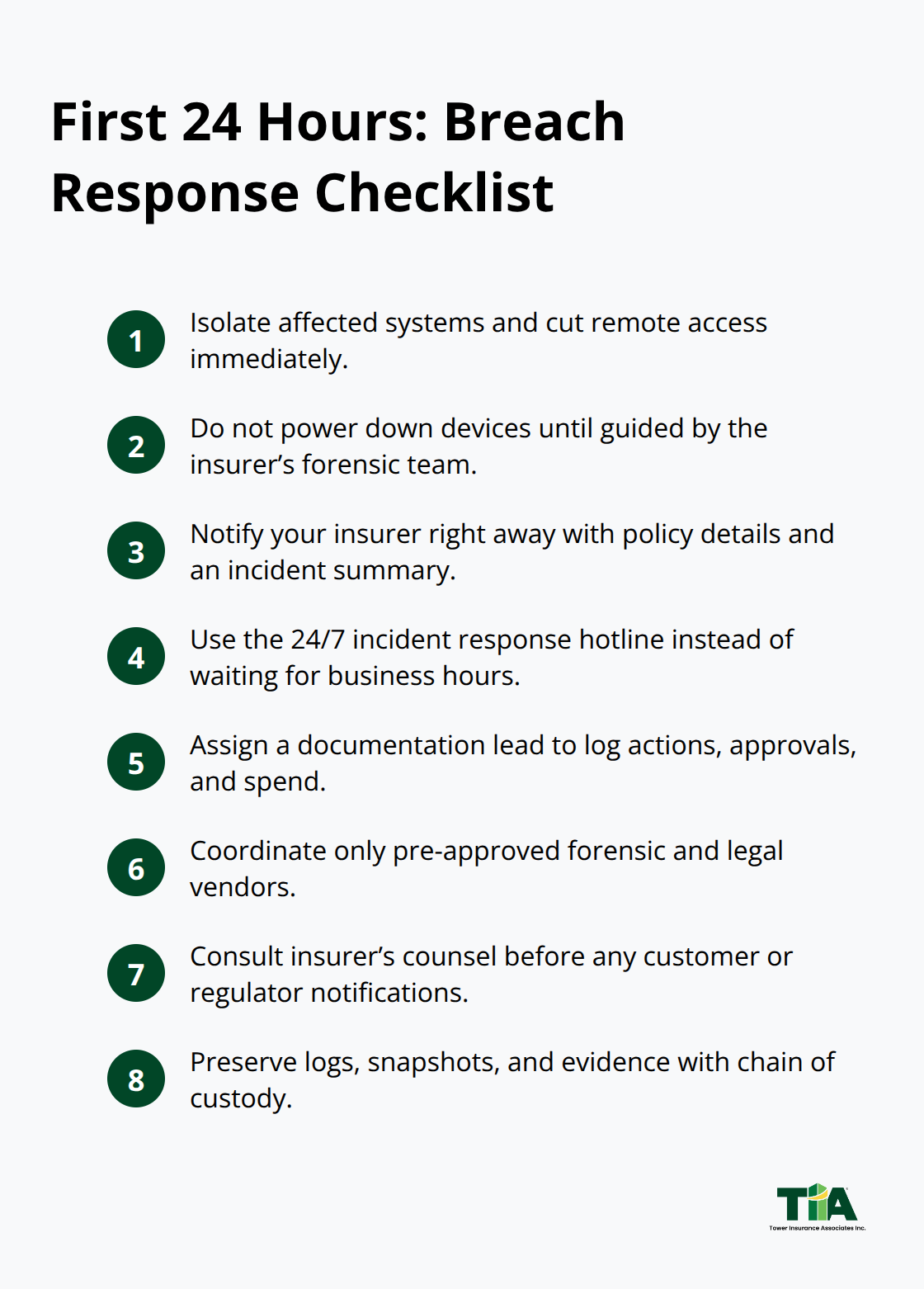
Many carriers offer 24/7 incident response hotlines specifically for after-hours breaches, so use them immediately rather than waiting for business hours.
Document every decision and expense from the start
Simultaneously, appoint one person as your documentation lead-this individual maintains a centralized log of all response decisions, timestamps, communications with the insurer, and every dollar spent on the incident. IBM Security’s 2023 Cost of a Data Breach report found that US organizations average $9.5 million in total breach costs, and insurers scrutinize documentation to determine which expenses qualify for coverage. A forensic investigation typically costs around $45,000 per incident according to recent claims data, and that expense only gets reimbursed if you’ve documented the insurer’s approval and worked with their approved vendors. Your documentation should capture the attack timeline, affected systems, number of records exposed, response actions taken, and all vendor communications before you file the formal claim.
Meet California’s notification deadlines and preserve evidence
California law requires you to notify affected individuals within 30 calendar days after discovering the breach. This timing matters to your insurer because delays can trigger additional penalties and regulatory fines that fall outside your policy’s coverage. Contact your insurer’s legal counsel before sending any notification to customers or regulators, as the wording affects your liability exposure and claim validity. Many cyber policies include crisis management and public relations support, so use these pre-approved resources rather than hiring external firms without carrier approval. If you hire vendors outside the insurer’s approved panel without permission, you risk having those costs excluded from your reimbursement.
Preserve evidence and quantify financial losses
Preserve all evidence with proper chain of custody-forensic investigators need unaltered logs, system snapshots, and communications with threat actors if ransom demands occurred. Your forensic report becomes the foundation for coverage determinations, so any gaps or procedural errors in evidence preservation can result in disputed claims. If your business experienced interruption, calculate revenue losses by comparing your profit trajectory before the attack to actual results during recovery, ideally with input from a forensic accountant. Document customer churn, additional operational expenses incurred during the outage, extended recovery costs, and any contractual penalties you faced. This financial documentation is essential because coverage disputes occur in approximately 30 percent of complex claims, and detailed loss calculations prevent underinsurance and claim denials.
Once you’ve stabilized your systems and documented the incident’s scope, the next phase involves working with forensic investigators and legal counsel to build a defensible claim that withstands carrier scrutiny and positions your business for full recovery.
Filing and Defending Your Cyber Claim
After you notify your insurer within the required 24 to 72 hours, the claims process shifts into a formal documentation phase that determines whether you receive full reimbursement or face coverage disputes. Your insurer will assign a dedicated claims handler and issue a reservation of rights letter outlining what they will and won’t cover based on your policy language. At this stage, your documentation becomes critical: submit a detailed incident timeline, system logs from before and during the attack, affected data inventory, response actions taken, vendor approvals, and itemized expenses. The insurer will request preliminary incident details within days, and any gaps or inconsistencies between your initial notice and subsequent submissions can trigger coverage denials.
Work with a cyber insurance attorney early
A cyber insurance attorney should review your claim before disputes arise, not after. The attorney examines the carrier’s interpretation of policy terms, warranties, and exclusions against your specific incident facts, catching issues before they become claim denials. Many Southern California businesses mistakenly hire forensic investigators or legal counsel outside their insurer’s approved vendor panel, only to discover those costs fall outside coverage. Your insurer maintains these panels specifically to control quality and cost, so coordinate all vendor selections with your claims handler before engaging anyone. If you must use an outside expert due to timing or expertise gaps, obtain written pre-approval from the insurer first.
Build your claim foundation with forensic investigation
Forensic investigation forms the foundation of your claim’s defensibility. Forensic investigators preserve evidence with proper chain of custody, analyze attack vectors, determine how long the attacker remained in your systems, and identify root causes. This report directly influences whether the insurer pays your claim in full or disputes coverage based on security control failures or negligence. For business interruption claims, quantify losses meticulously: calculate revenue losses by comparing pre-attack profit momentum to actual post-incident results, document customer churn with names and contract values, and track every additional operational expense incurred during recovery. A forensic accountant strengthens these calculations and provides the documentation that prevents carriers from disputing your loss amounts.
Navigate coverage disputes and settlement negotiations
Coverage disputes occur in approximately 30 percent of complex claims, and most disputes center on either the scope of what qualifies for reimbursement or whether security control breaches void coverage entirely. When the insurer issues an initial settlement offer, have your coverage attorney review the calculation against your documented losses and the policy’s specific terms. Negotiating disputed amounts typically requires mediation or settlement conferences, and carriers often increase initial offers once they see detailed financial substantiation. If regulatory investigations arise from the incident, defense costs generally count against your policy limits, so clarify with your claims handler whether investigation expenses reduce available funds for other claim categories.
Understand payment timelines and subrogation
Upon settlement, expect payment within approximately 30 days, sometimes with advances for emergency response costs. The insurer may pursue subrogation afterward, seeking recovery from third parties like software vendors or service providers whose failures contributed to the breach, though this typically does not affect your reimbursement timeline.
Final Thoughts
A cyber incident in Southern California demands speed, documentation, and expert guidance. The businesses that recover fastest act within the first 24 hours, notify their insurer immediately, and preserve evidence methodically. Your cyber liability claim succeeds or fails based on decisions made in those critical opening hours, not months later during disputes.
Treat incident preparedness as a business priority, not an afterthought. Map your data flows to understand what customer information you hold and where it lives. Implement multi-factor authentication across remote access and privileged accounts, deploy endpoint detection and response tools, and conduct regular vulnerability scans-these security controls reduce your breach risk substantially and lower your cyber insurance premiums by 10 to 25 percent. Train your staff on phishing and social engineering tactics, since business email compromise attacks have surged 300 percent in the Inland Empire. Maintain encrypted backups with offline copies so you can recover quickly if ransomware strikes. Create a documented incident response plan with clear roles, communication protocols, and decision-making frameworks, then test it annually with tabletop exercises.
Your cyber liability policy should align with your actual data exposure and California’s strict privacy requirements. Healthcare practices need coverage limits starting around $2 million, while retail operations processing payment cards require PCI DSS compliance built into their policies. We at Tower Insurance Associates, Inc. understand the unique risks facing Riverside and LA businesses, and our team acts as your trusted local adviser when you need to review your cyber liability coverage or navigate a claim with our LA cyber claims guide.
Disclaimer: This blog post is for general informational purposes only and does not represent actual coverage, policy terms, or legal requirements. Insurance details vary by individual and jurisdiction. Please consult a licensed insurance professional for advice specific to your situation.

