Cyber attacks against small and medium-sized businesses have become routine, not exceptional. Ransomware, data breaches, and phishing schemes now target SMBs with alarming frequency because attackers view them as easier targets than large enterprises.
At Tower Insurance Associates, Inc., we’ve seen firsthand how cyber liability for SMBs can mean the difference between recovery and closure. This guide walks you through concrete defenses and insurance strategies that actually work.
How Bad Is the Cyber Threat to Your Business Right Now?
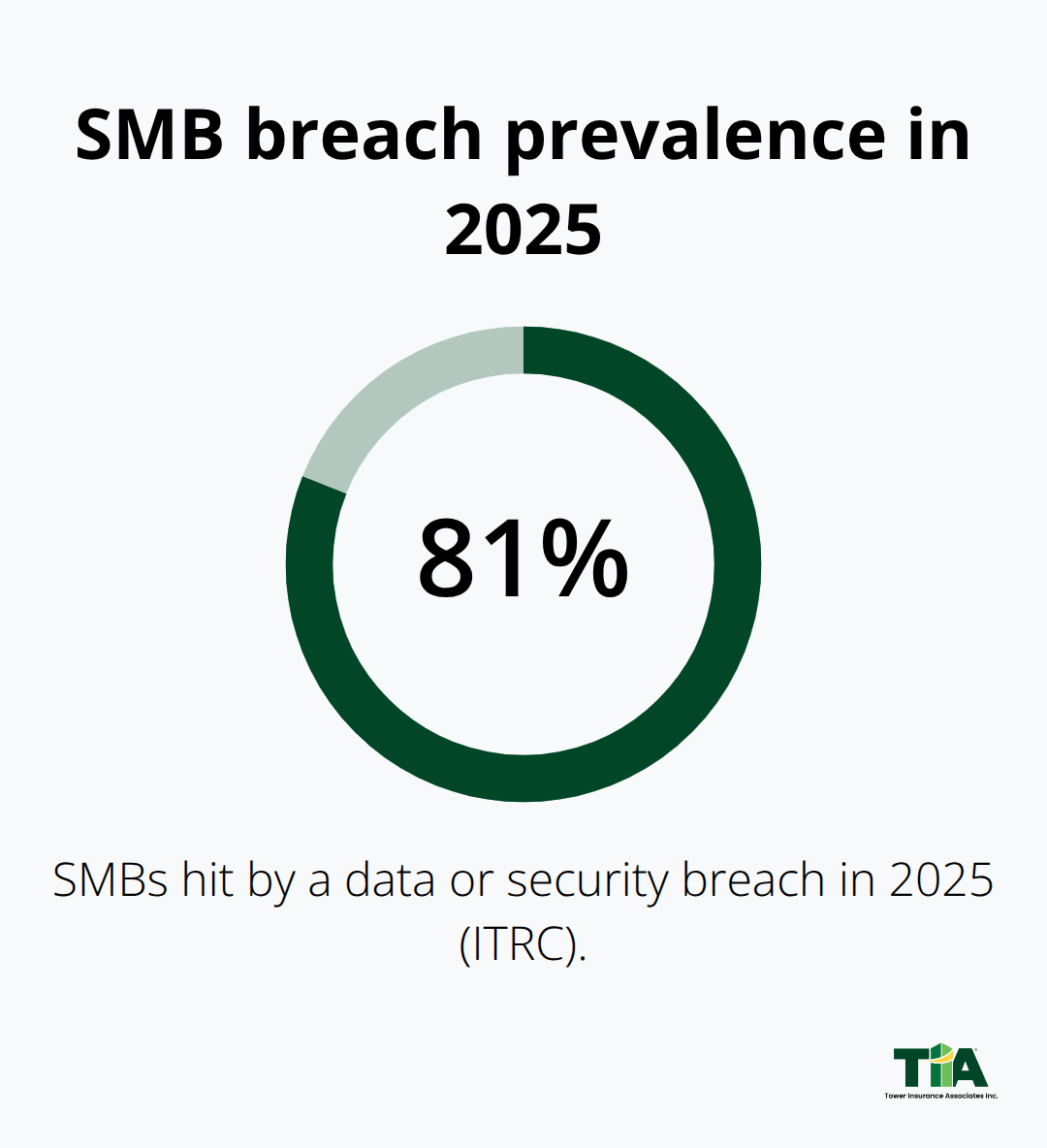
The numbers tell you exactly why SMBs face relentless attacks. According to the Identity Theft Resource Center’s 2025 Business Impact Report, 81% of small businesses were hit by a data or security breach this year. That’s not a fringe risk anymore-it’s the norm. When these attacks land, the financial hit is severe. More than half of the SMBs hit by cyber incidents reported losses between $250,000 and $1,000,000.
For a business running on thin margins, a single incident can force you to raise prices, cut staff, or shut down entirely. The SBA reports that employee actions and work communications cause the majority of SMB data breaches, which means your team is both your strongest asset and your biggest vulnerability point.
Ransomware Attackers Now Exfiltrate Before They Encrypt
Ransomware tactics have shifted dramatically in 2026. Attackers no longer just encrypt your files and demand payment-they steal your data first, then encrypt it, and impose impossibly short deadlines to pay. This two-pronged assault eliminates negotiation and stalling. The threat accelerates at scale. Projections show an attack occurring every two seconds by 2031, according to Astra Security. Right now, the average downtime from a ransomware attack runs about 21 days, during which your business generates zero revenue while costs pile up. Your backup strategy directly determines whether you survive this. Offline, immutable backups that you test regularly aren’t optional-they’re your lifeline. If your backups connect to your network or sit in the same cloud tenant where attackers gain access, they become worthless when you need them most.
Phishing Attacks Exploit Human Judgment, Not Just Technology
Phishing remains the most successful attack vector because it targets human judgment rather than just technology. In 2025, AI-enabled phishing and credential theft surged 160% according to IT Pro, making attacks far more personalized and convincing. Deepfake-related fraud has also hit roughly half of organizations, with attackers impersonating executives to authorize wire transfers. These aren’t generic mass emails anymore-they’re targeted, contextual, and designed to bypass your instincts. Employee training works, but only if it’s specific and repeated. Generic training that teaches people to spot obvious red flags misses the point. Your team needs to learn that legitimate-looking requests from known contacts, correct grammar, and urgent tones all signal danger. The SBA emphasizes that training on identifying phishing, avoiding suspicious downloads, and safe browsing practices directly reduces breach likelihood. One trained employee who stops and reports a suspicious message can prevent a breach that costs six figures to remediate.
Your Defenses Must Match the Speed of Modern Attacks
The 2026 SMB threat landscape is dominated by AI-powered, highly targeted attacks that operate at speed and scale. Attackers move fast, and your response speed must match theirs. Standard security measures that worked five years ago no longer cut it. You need defenses that detect threats in real time, isolate compromised systems immediately, and restore operations from clean backups without delay. This is where the gap between awareness and action widens for most SMBs. You know the threats exist, but implementing the right controls-multi-factor authentication across all accounts, endpoint detection and response on every device, immutable offline backups, and 24/7 monitoring-requires investment and discipline. The cost of these defenses is far lower than the cost of recovery, legal fees, notification expenses, and lost revenue after an attack hits.
What Cyber Liability Insurance Actually Covers
Cyber liability insurance splits into two distinct protection buckets: first-party claims and third-party claims. First-party coverage pays for your own losses: data restoration costs, business interruption when systems go down, ransomware payments if you choose to pay, and crisis communication expenses to notify customers and manage your reputation. Second-party coverage protects you against claims from others-your customers, business partners, or regulators-including legal defense costs, settlements, and regulatory fines.
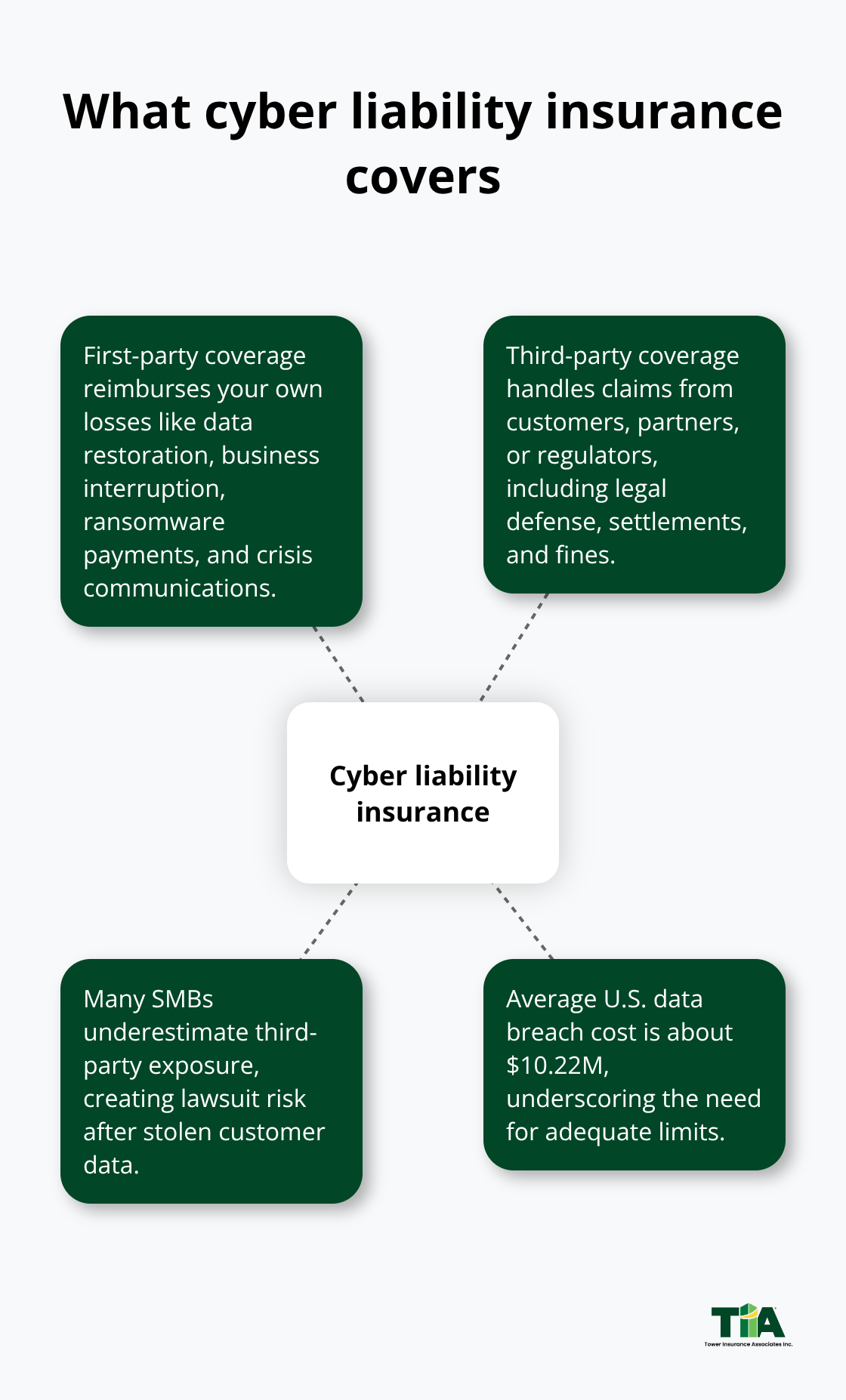
Most SMBs focus only on first-party costs and ignore second-party exposure, which leaves them vulnerable to lawsuits from customers whose data was stolen in your breach. The average cost of a data breach in the U.S. reaches about $10.22 million according to IBM, and cyber liability insurance covers two primary elements: first-party claims and third-party claims.
Insurers Now Demand Proof of Your Security Controls
Insurers have shifted away from assumption-based pricing and now demand proof that you’ve implemented specific security controls before they’ll issue a policy or offer competitive rates. Multi-factor authentication on all critical accounts, endpoint detection and response on every device, immutable offline backups that you test quarterly, and a documented incident response plan are no longer nice-to-haves-they’re the baseline that insurers expect. If you can’t demonstrate these controls, you’ll face higher premiums, larger deductibles, or outright coverage denial. Conversely, visible security investments reward you with lower premiums. Insurers view MFA, regular employee training, automated patch management, and strong backup procedures as evidence that you take threats seriously and won’t file frivolous claims. This creates a powerful incentive: the more robust your defenses, the less cyber insurance costs you.
Calculate Your Coverage Limits Based on Real Exposure
Choosing coverage limits requires honest assessment of what you’d lose in a worst-case breach, not guessing. Calculate your annual revenue, the amount of customer data you hold, the cost to notify customers (state laws typically require notification within 30 to 60 days), potential regulatory fines based on your industry, and the cost to restore operations from backups. If you process payment cards, you face PCI-DSS compliance requirements and fines up to $100,000 per month for violations. If you handle healthcare data, HIPAA violations carry fines up to $1.5 million per violation category per year. If you operate in California or similar states with strict data privacy laws, notification and credit monitoring costs alone can exceed $500,000 for a moderate breach. Try setting your first-party coverage limit high enough to cover 90 days of lost revenue plus restoration costs. Try setting your second-party limit high enough to cover potential legal defense and settlements-typically $1 to $5 million depending on your customer base size and data sensitivity. Underinsuring creates a false economy: you save $200 a month on premiums but expose yourself to six-figure gaps when an incident occurs.
Work With an Independent Agent to Match Coverage to Your Business
An independent insurance agent can help you navigate the complexity of cyber liability policies by assessing your specific data exposure, industry compliance obligations, and vendor relationships-then matching you with carriers that offer the right coverage at competitive rates. This personalized approach matters because off-the-shelf policies often miss critical gaps. Your agent can also help you understand what your current homeowners or general liability policies exclude (spoiler: they exclude cyber incidents entirely) and how cyber liability fills those gaps. When you’re ready to purchase coverage, your agent advocates for you during claims, ensuring the insurer honors the policy terms and pays what you’re owed.
How to Build Your Security Foundation Before an Incident Hits
Waiting for a breach to happen and then scrambling to respond costs far more than preventing one in the first place. The most effective SMBs don’t just buy cyber insurance and hope for the best-they systematically identify weaknesses, close them, and measure progress. Start with a security audit that maps what data you actually store, where it lives, who can access it, and what controls protect it. This isn’t theoretical. The SBA emphasizes that a cybersecurity risk assessment identifies real vulnerabilities and creates a practical action plan with concrete training and security measures.
Map Your Data and Close the Biggest Doors First
Free tools exist to help you start: the FCC Small Biz Cyber Planner 2.0 walks you through a structured assessment, and CISA offers free vulnerability scans specifically for small businesses to test your actual exposure without cost. Once you complete an audit, prioritize ruthlessly. Don’t try to fix everything at once. Instead, close the biggest doors first within 30 days: enable multi-factor authentication on all critical accounts like email, financial systems, and payroll platforms.
Remove legacy authentication protocols that attackers exploit to bypass modern security. Inventory every administrator account in your systems and disable ones that no longer have a business purpose. Confirm that your backups are truly immutable and stored offline-if they live in the same cloud tenant where an attacker gains access, they become useless when you need them most.

Train Employees to Spot and Report Threats
Your employees either stop attacks or enable them, so training must be specific and repeated, not generic. The SBA reports that employee actions and work communications cause the majority of SMB data breaches, which means one trained person who spots a phishing message before clicking can prevent a breach that costs hundreds of thousands to remediate. Effective training teaches people that requests from known contacts with correct grammar and urgent tones signal danger, not legitimacy.
Deepfake fraud now targets roughly half of organizations with attackers impersonating executives to authorize wire transfers, so your finance and executive teams need tabletop drills where you practice responding to suspicious transfer requests without panicking. Run a simple CEO-fraud scenario quarterly where someone claims to be the owner requesting an immediate wire transfer-see who questions it and who approves it, then coach accordingly.
Test Your Incident Response Plan and Backups Regularly
Build an incident response plan that you actually test before you need it. Document who to contact when an incident occurs, how to isolate compromised systems without destroying evidence, which systems you’ll restore first, and how you’ll notify customers and regulators. Assign specific people to specific roles so there’s no confusion during a crisis. Test your backup restoration quarterly to confirm you can recover from a clean copy in the timeframe your business requires.
Insurers now demand evidence of these controls before issuing policies at competitive rates, so implementing them also directly lowers your cyber insurance premiums while improving your actual resilience.
Final Thoughts
Your defenses matter, but attackers operate at scale and exploit vulnerabilities faster than you can patch them, which is why cyber liability for SMBs becomes non-negotiable. Standard business policies exclude cyber incidents entirely, leaving you exposed to costs that can exceed your annual revenue in a single attack. When a breach hits, you face immediate expenses: forensic investigation, notification costs within legal timeframes, credit monitoring services, legal defense, and potential regulatory fines based on your industry. A moderate breach costs $250,000 to $1,000,000 in direct expenses alone according to ITRC 2025 data, and without cyber liability insurance, you pay this from cash reserves or go into debt.
Cyber liability insurance also covers business interruption when systems go down, meaning you receive compensation for lost revenue during recovery. Ransomware attacks average 21 days of downtime, so if your business generates $50,000 weekly, that’s over $1 million in lost revenue before you’re operational again. Cyber insurance covers this gap and keeps payroll flowing while you restore operations. Proper coverage allows you to focus on recovery instead of bankruptcy.
Implement the security controls outlined in this guide, then partner with an insurance professional who understands your specific exposure. We at Tower Insurance Associates, Inc. help SMBs across California assess their cyber risk and find coverage that matches their actual needs at competitive rates. Visit Tower Insurance Associates, Inc. to discuss your cyber liability coverage today.
Disclaimer: This blog post is for general informational purposes only and does not represent actual coverage, policy terms, or legal requirements. Insurance details vary by individual and jurisdiction. Please consult a licensed insurance professional for advice specific to your situation.

