Small businesses in California face a growing wave of cyber attacks, with threats ranging from ransomware to data breaches that can cripple operations overnight. At Tower Insurance Associates, Inc., we’ve seen firsthand how a California cyber risk assessment can reveal critical vulnerabilities before they become costly problems.
This guide walks you through identifying your biggest security gaps, strengthening your defenses, and protecting your business with the right coverage and response strategies.
What Threats Actually Target California Small Businesses
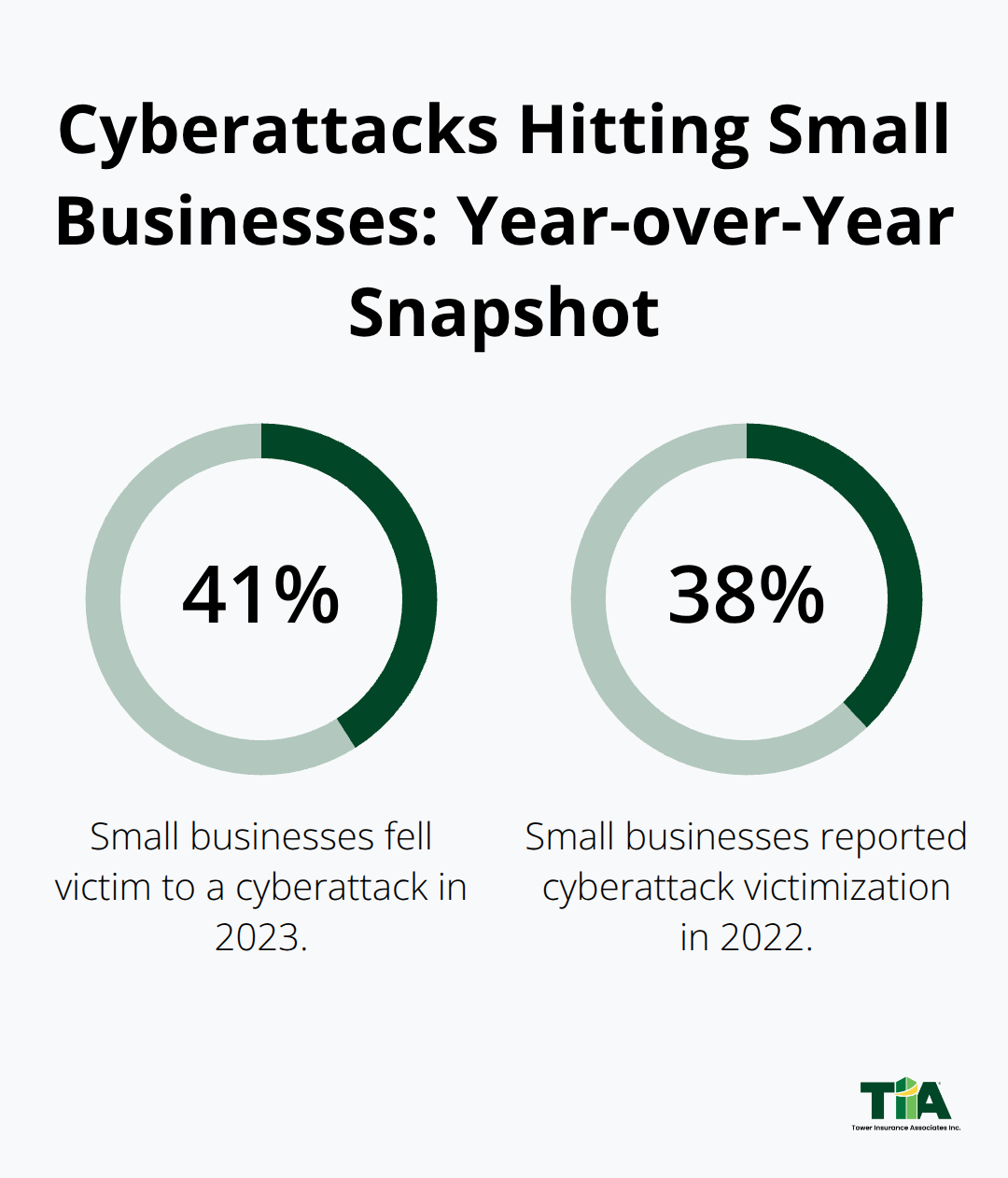
Ransomware, credential stuffing, and unpatched systems represent the top attack vectors for small businesses in 2024, according to CrowdStrike’s threat intelligence. Forty-one percent of small businesses fell victim to a cyberattack in 2023, up from 38% in 2022.
The financial stakes are severe: the global average cost of a data breach is $4.44 million. California’s regulatory landscape adds another layer of complexity. The California Consumer Privacy Act and its successor, the California Privacy Rights Act, impose strict obligations on businesses that collect personal data from California residents. If your business meets certain thresholds-processing 250,000 or more California residents’ information, deriving 50 percent or more of revenue from selling data, or processing sensitive personal information of 50,000 or more residents-you face mandatory cybersecurity audits by April 1, 2028, 2029, or 2030 depending on revenue size. The CPRA also requires risk assessments for high-risk data processing, with compliance deadlines that began January 1, 2026. These aren’t abstract compliance checkboxes; they carry real penalties and expose your business to lawsuits if you mishandle resident data.
Why Attackers Focus on Small Businesses
Cybercriminals target small businesses because they assume you lack robust defenses. Fifty-nine percent of organizations report feeling understaffed in cybersecurity, which means most small business owners juggle IT responsibilities without dedicated security personnel. Attackers know this. The average time to breach a small business network dropped to 62 minutes in 2023 from 84 minutes in 2022, according to CrowdStrike. Human error remains the primary entry point: roughly 68 percent of incidents stem from phishing and employee mistakes. Your staff represents both your strongest asset and your biggest vulnerability. Seventy-eight percent of people reuse the same password across accounts, creating a domino effect when credentials get compromised. This is why credential stuffing attacks succeed so frequently against small businesses-attackers buy stolen password lists and test them against your systems. California’s location makes you a higher-value target. Your proximity to tech companies, venture capital, and high-income residents means attackers assume your data has resale value.
California’s Compliance Demands Are Strict
The CCPA grants California residents four core rights: the right to know what data you collect, the right to delete their information, the right to opt out of data sales, and the right to non-discrimination when exercising these rights. The CPRA expanded these rights to include data correction and limits on use of sensitive information. These aren’t optional courtesies. The California Privacy Protection Agency, established to enforce CPRA violations starting July 1, 2023, has authority to impose civil penalties.
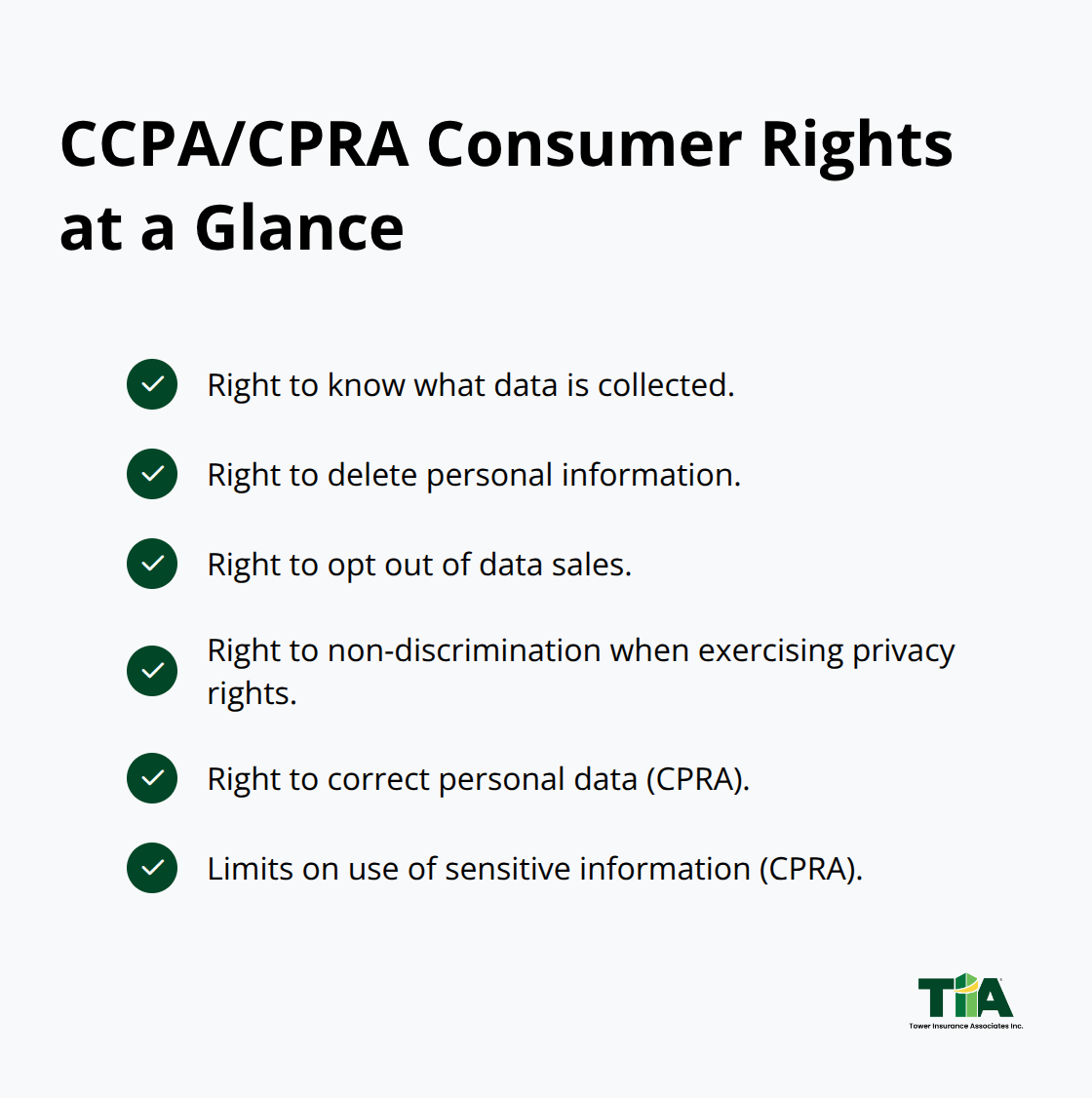
Private citizens can also sue for data breaches involving unencrypted personal information caused by inadequate security, with statutory damages up to $750 per incident. You must respond to consumer rights requests within 45 calendar days. You need at least two designated channels for consumers to submit requests, whether that’s a toll-free number, website form, or email. If you use automated decision-making technology to make significant decisions (hiring, lending, housing, education), you must disclose this pre-use and allow opt-outs. These requirements demand that you know exactly what data you hold, where it lives, who can access it, and how you protect it. Understanding your current security posture through a cyber risk assessment reveals where your defenses fall short against these regulatory obligations and the threats that exploit them.
How to Map Your Data and Security in Three Steps
Start With a Complete Data Inventory
A cyber risk assessment isn’t a document you commission once and file away. It’s an operational inventory that forces you to answer hard questions: What data does your business actually hold? Where does it live? Who can access it? What happens when someone tries to steal it?
List every system, device, and location where California resident data flows through your business. This includes customer databases, email servers, cloud storage, payment processors, backup systems, and paper files in filing cabinets. CrowdStrike’s 2024 research shows that 57 percent of breach victims were compromised through unpatched known vulnerabilities, which means attackers often exploit systems you didn’t even realize needed attention.
Map your high-value assets first: customer payment information, personal identifiers, health records, financial data, and anything that could trigger CCPA or CPRA obligations. If you process 250,000 or more California residents’ information or derive 50 percent of revenue from selling data, you’ll face mandatory cybersecurity audits by 2028, 2029, or 2030 depending on your revenue tier. That audit will require an independent third party to assess 18 cybersecurity components across your entire operation, so knowing your data landscape now prevents scrambling later.
Test Your Current Security Controls Honestly
Evaluate what security controls you actually have in place versus what you think you have. Many small business owners assume their IT vendor or cloud provider handles security, only to discover critical gaps when a breach occurs.
Test your defenses honestly: Do you have multi-factor authentication enabled on all accounts? CrowdStrike data shows that only 46 percent of small businesses have implemented MFA, yet MFA prevents 99.9 percent of account-based attacks. Are your systems patched regularly, or do updates pile up for months? Do employees use unique, complex passwords, or do they reuse the same credentials across multiple accounts? Seventy-eight percent of people reuse passwords, making credential stuffing attacks devastatingly effective.
Do you have endpoint protection on every device, including laptops used for remote work? Can you isolate an infected machine within minutes, or would an attacker have unrestricted movement through your network for hours? Speed matters: the average time to breach a small business network dropped to 62 minutes in 2023 from 84 minutes in 2022.
Conduct a Structured Vulnerability Assessment
Perform a structured vulnerability assessment to identify gaps between your current controls and what the threat landscape demands. Test your network for exploitable weaknesses, check whether your Wi-Fi is properly encrypted and password-protected, and review user access permissions to confirm employees only reach data they need.
Verify that backup systems are isolated and regularly tested for recovery. Document which systems hold sensitive data and whether that data is encrypted both in transit and at rest. Review your incident response procedures: do you have a written plan, or just vague assumptions about what you’d do during an attack? NIST’s framework covers four phases-Preparation, Detection and Analysis, Containment and Eradication and Recovery, and Post-Incident Activity-and small businesses that follow this structure recover faster and with fewer cascading damages.
Assess your physical security too: improper document disposal accounts for 14 percent of data breaches from physical attacks according to CrowdStrike, so shredding protocols and visitor access controls matter.
Prioritize Fixes by Risk Level
Create a remediation roadmap that prioritizes fixes by risk level and business impact. High-risk items like unpatched critical systems and missing MFA on admin accounts get fixed immediately. Medium-risk gaps like outdated antivirus software or weak password policies get addressed within 30 to 60 days. Lower-priority improvements like network segmentation enhancements extend across a longer timeline.
This assessment becomes your baseline for measuring progress and your foundation for compliance with California’s growing cybersecurity audit and risk assessment requirements. Once you understand where your vulnerabilities live, you can implement the specific security controls that actually stop attackers from reaching your most valuable data.
Protecting Your Business with Security Controls and Insurance
Your vulnerability assessment identified the gaps. Now you need to close them with security controls that actually stop attackers from reaching your data. The controls that matter most for small businesses are straightforward: multi-factor authentication, patch management, endpoint protection, and network segmentation.
Enable Multi-Factor Authentication First
MFA prevents 100% of automated attacks, yet only 46 percent of small businesses have implemented it. Start there. Activate MFA on every admin account immediately, then roll it out to all employee accounts within 30 days. This single control stops credential stuffing attacks cold because even if an attacker has your password, they cannot access your account without the second factor.
Establish a Patch Management Schedule
CrowdStrike found that 57 percent of breach victims fell victim to unpatched known vulnerabilities, meaning attackers exploit systems you already know are vulnerable but haven’t fixed. Set a schedule: critical patches within 48 hours, high-priority patches within two weeks, routine patches within 30 days. Test patches in a non-production environment first to avoid breaking critical systems.
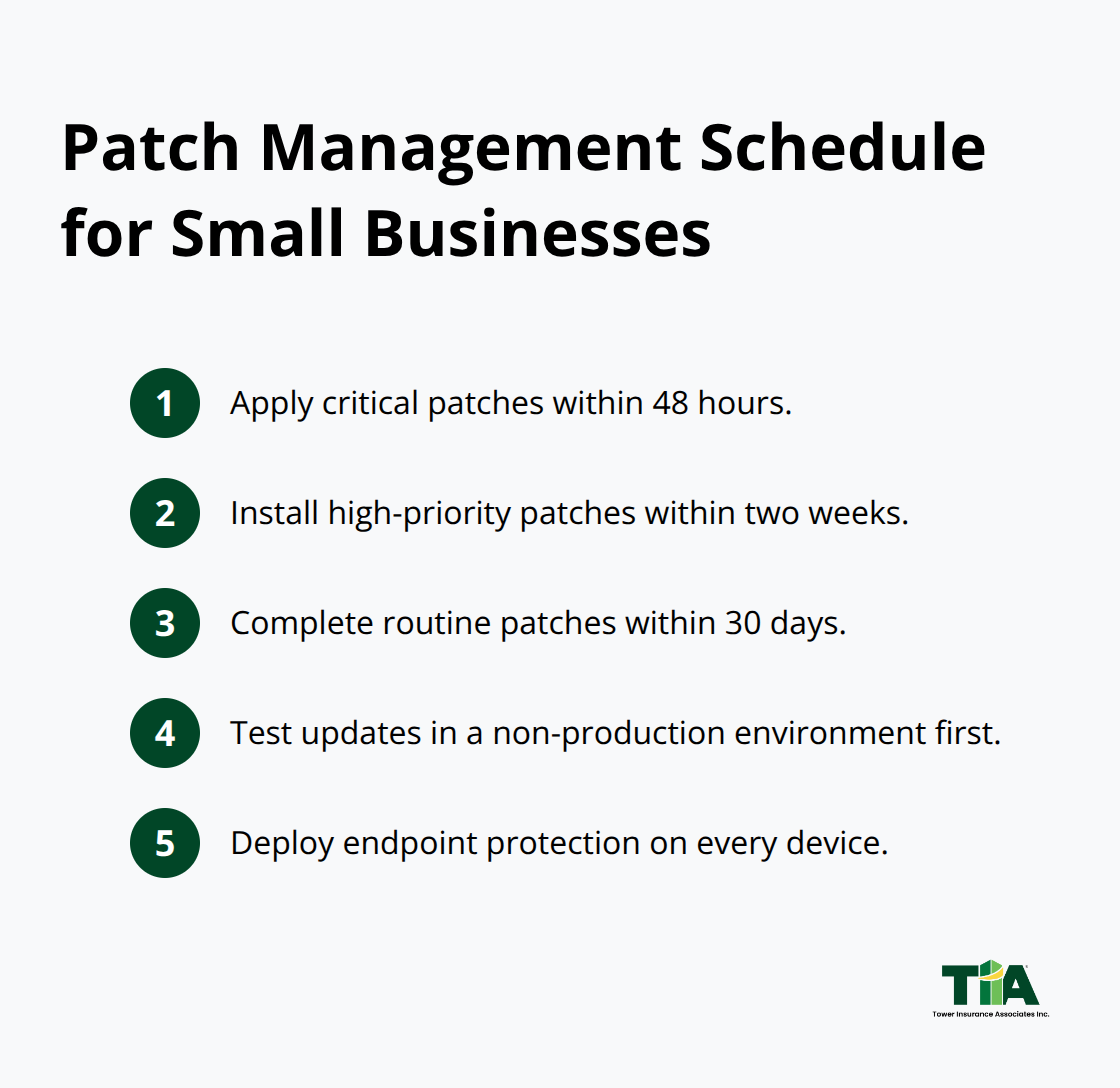
Deploy endpoint protection software on every device, including remote work laptops and phones that access business data.
Isolate your payment card processing systems from other programs and networks so a breach of your general network cannot reach your payment infrastructure. Encrypt sensitive data both in transit and at rest, particularly customer payment information and personal identifiers. California’s CCPA and CPRA create liability if unencrypted personal information is breached due to inadequate security, with statutory damages up to $750 per incident, so encryption is not optional.
Create a Documented Incident Response Plan
Develop your incident response plan before you need it. Your plan should follow NIST’s four-phase framework: Preparation covers your baseline controls, backups, and team training; Detection and Analysis means you know how to identify a breach and gather evidence; Containment and Eradication involves isolating affected systems and removing the attacker; Post-Incident Activity includes recovery, notifications, and lessons learned.
Assign specific roles: who identifies a breach, who communicates with customers, who contacts law enforcement, who manages the technical response. Test this plan annually through tabletop exercises so your team moves decisively if an actual breach occurs. Speed matters. CrowdStrike’s data shows the average time to breach a small business network is 62 minutes, so your team must recognize suspicious activity and isolate affected machines within that window.
Maintain regular, tested backups of critical data stored offline or in isolated cloud environments so you can recover operations even if ransomware encrypts your primary systems. Document everything: which systems you backed up, when backups occurred, and whether recovery works.
Cyber Liability Insurance Closes the Gap
Cyber liability insurance bridges the gap between perfect controls and real-world attacks. Policies that cover breach response costs, regulatory fines, notification expenses, and business interruption losses protect your business when attacks succeed despite your best efforts. California’s regulatory environment makes cyber liability coverage essential because CCPA and CPRA violations carry penalties from the California Privacy Protection Agency, and private lawsuits for data breaches can exceed your internal resources to defend.
Select a policy that includes incident response support so you have legal and forensic experts available immediately when a breach occurs, not weeks later when damage compounds. Coverage should address your specific risk profile: if you process payment cards, verify your policy covers PCI compliance costs; if you hold health information, verify it covers HIPAA breach notification; if you use automated decision-making technology for significant decisions, verify your policy covers CPRA compliance costs. Tower Insurance Associates, Inc., an independent insurance agency in Culver City with a full suite of commercial coverages including cyber liability, can help you find tailored coverage that matches your business needs and budget.
Final Thoughts
A California cyber risk assessment reveals vulnerabilities that attackers actively exploit, but the assessment itself is only the starting point. You now understand your data landscape, tested your security controls, and identified gaps between your current defenses and what threats demand. The next phase is execution: implement MFA across all accounts, establish a patch management schedule, deploy endpoint protection, and document your incident response plan.
Compliance deadlines approach fast. If you process 250,000 or more California residents’ information or derive 50 percent of revenue from selling data, mandatory cybersecurity audits begin in 2028, and risk assessments for high-risk data processing already required compliance by January 1, 2026. Waiting until audit season to strengthen your security posture means scrambling under pressure and potentially failing to meet regulatory standards. Start now.
Your security controls and incident response plan form a strong foundation, but they cannot prevent every attack. Cyber liability insurance fills that gap by covering breach response costs, regulatory fines, notification expenses, and business interruption losses when attacks succeed despite your best efforts. We at Tower Insurance Associates, Inc. help California small businesses find cyber liability coverage tailored to their specific risks and budgets, and you can discuss your cyber liability needs with a local adviser who understands California’s regulatory demands and the real costs of breaches.
Disclaimer: This blog post is for general informational purposes only and does not represent actual coverage, policy terms, or legal requirements. Insurance details vary by individual and jurisdiction. Please consult a licensed insurance professional for advice specific to your situation.

